Being an IT administrator is a tough job, especially when you are a department of one. You don’t have anyone else to help you, and without that support and backup it can make things challenging. And, there are many people in this situation.
Dirk Paessler, CEO of Paessler, estimates that there are more than one million solo IT admins around the world. When you are working as a department of one, you need tools, tips and tricks that help you to be as effective and efficient as possible. Here are five tips that can help make life easier for the solo IT admin.
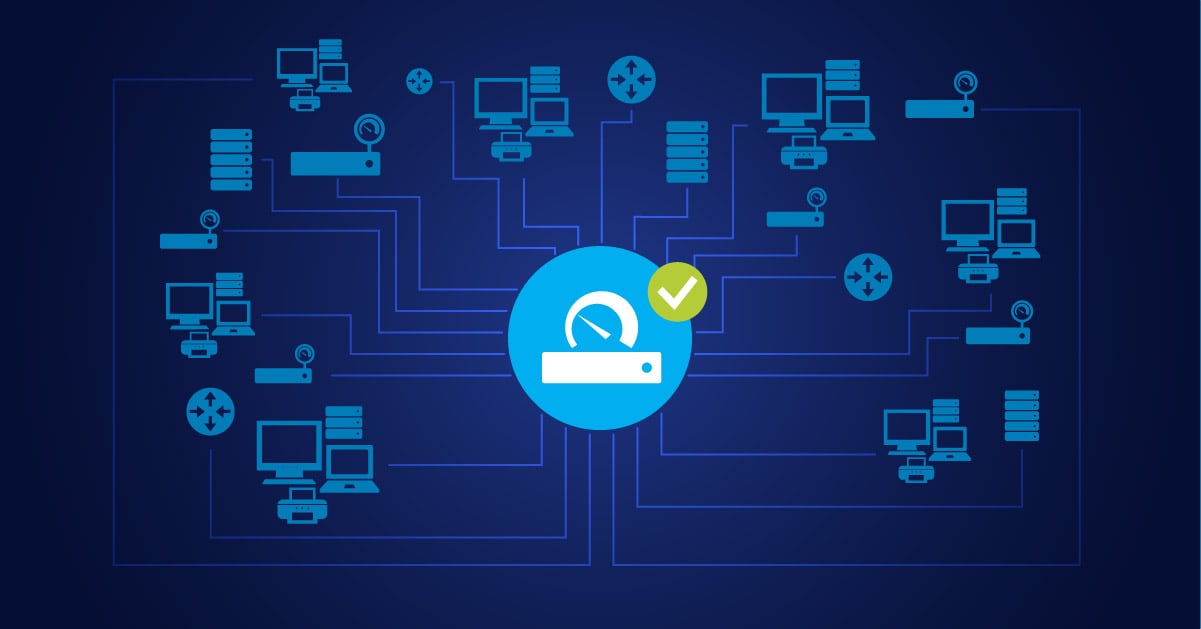
Daily Health Checks
These “check in” scans can be scheduled on different systems to run regularly to give you an overall view of how a given system is running. They can also alert you if something is not working correctly or is running close to its limit or threshold. Receiving a daily health check report can be part of an IT admin’s morning routine, giving them helpful status information to start off their day.
Real-Time Monitoring to Help You in Advance 
In addition to daily checks, real-time monitoring can give you instant status information on the network, security tools, as well as Quality-of-Service (QoS) and bandwidth utilization levels.
This information can be especially important when you have a big event planned, such as a new product launch, a tradeshow, a webinar or another major news event that may bring a large number of people to your website and/or network.
iBandwidth is measured as the amount of data that can be transferred from one point to another within a network in a specific amount of time. Typically, bandwidth is expressed as a bitrate and measured in bits per second (bps). It refers to the transmission capacity of a connection and is an important factor when determining the quality and speed of a network. Read more ...
A Clear, Defined Security Policy
Having a clearly defined security policy that you can share with everyone in the organization helps prevent a lot of issues. It is much easier when everyone knows “what the rules are” regarding IT security in the company. This makes enforcement of the rules much easier, and helps to prevent any issues around “gray areas” of what is (or is not) an acceptable practice.
Advanced Notice on People Who Join or Leave the Company 
Along with the security policy, it is also important to get advanced notice from your company on any employees who are going to join or leave the organization. For “joiners” this will enable you to get systems and IT tools set up in advance so they can properly access the network and other IT resources with the proper security credentials. For “leavers” it is important to know in advance so that you can turn off access to network and IT resources as soon as the employee leaves the company. This is imperative to avoid any security violations or risk having important company information shared improperly by a former employee.
SaaS-Based Systems
There are many advantages to SaaS-based systems, and they continue to be more widely used in organizations around the world. SaaS makes maintenance and monitoring easier, as much of this is done dynamically by the provider in real time. You no longer have to worry about servers, switches or routers having the latest version of firmware, software, or security patches.
Also, the redundancy of the SaaS provider helps to keep systems running - disaster recovery is often “built in” from the provider so there is less to worry about on-premise at your company. Your main concern can be keeping your WAN connection to the cloud so that you can access SaaS-based resources, and this can be done from multiple locations (or remotely) so you are not nearly as vulnerable if there is an issue with power or network access in your building.
In all, being an IT department of one has its advantages and challenges, but with advanced planning and help from some useful tools and best practices, you can keep on top of your network and systems to protect their integrity and free up your time for more strategic projects that can help your organization.
 Published by
Published by