Although bandwidth isn't as strictly limited as it was some time ago, the perception of seemingly unlimited bandwidth can trigger problems in productive environments.
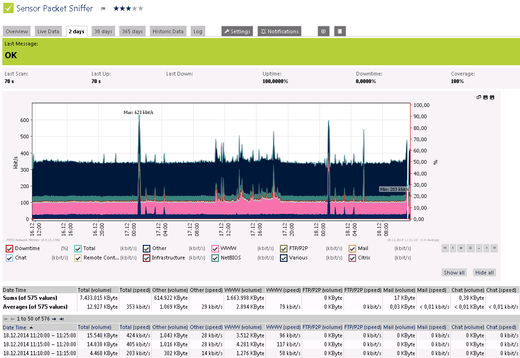
If your network devices don't support SNMP or flow monitoring, or you need to differentiate bandwidth usage by network protocol and/or IP addresses, packet sniffing is the way to go. To calculate bandwidth usage, the Packet Sniffer Sensor looks at every single data package that travels through your network. PRTG analyzes the packets passing the network card of a PC or the monitoring port of a switch; you can also use remote probes to set up packet sniffers anywhere in your network.
In detail the Packet Sniffer Sensor enables you to keep an eye on the following channels:
- Web for internet web traffic,
- File Transfer for traffic caused by FTP (File Transfer Protocol),
- Mail for internet email traffic,
- Chat for traffic caused by chat and instant messaging,
- Remote Control for traffic caused by remote control applications, such as RDP, SSH, Telnet, or VNC,
- Infrastructure for traffic caused by network services, such as DHCP, DNS, Ident, ICMP, or SNMP,
- NetBIOS for traffic caused by NetBIOS communication,
- Citrix for traffic caused by Citrix applications, and
- Other Protocols for traffic caused by various other protocols via UDP and TCP.
Packet sniffing not only allows you to measure the total bandwidth usage: You can also let PRTG break down the traffic by IP address, port, protocol and other parameters. The results are shown in Toplists, which offer three predefined bandwidth categories for each sensor:
- Top Connections shows bandwidth usage by connection,
- Top Protocols shows bandwidth usage by protocol, and
- Top Talkers shows bandwidth usage by IP address.
For more information on bandwidth monitoring via packet sniffing in general and the Packet Sniffer Sensor in detail, please have a look at the PRTG manual.
All Sensors of the Week
You have missed other articles of our "Sensors of the Week" blog series? Just take a look at the last 10 sensors:
 Published by
Published by