The attack on a water company in Oldsmar, Florida, is an almost textbook illustration of the security flaws that still prevail in many critical infrastructures. The lack of damage from the attack was a lucky coincidence rather than due to a thorough security concept. The incident underscores the need for intelligent, real-time monitoring in critical infrastructure.
This is a guest article by Klaus Mochalski, CEO of Rhebo.
In early February 2021, the control system of the water utility in Oldsmar, USA, fell victim to an external tampering attempt. According to the utility's supervisor, a hacker gained access to the central control system around 1:30pm on February 5. The hacker took control of the screen and increased the addition of sodium hydroxide (also known as lye) by a factor of hundreds. The chemical is used in water treatment to regulate the acidity of drinking water. The water utility serves about 15,000 residents in the county as well as local stores and businesses.
According to management, the hacker had infiltrated the system through remote access. This technology is regularly used by the staff, as well as service providers, to access system controls for water supply and treatment via authorized accounts. The active operator had briefly recorded remote access to the system earlier that morning, as Tampa Bay Times reported on February 8. According to the operator, however, he had assumed that this was his supervisor, who regularly inspects the system. It is still unclear whether the attacker gained access via the supervisor's access. If not, the installed cybersecurity system clearly lacks the ability to reliably identify new, unauthorized network participants.
Discovery By Accident
 The fact that the manipulation was discovered in time was a coincidence. When the attacker accessed the system again at 1:30pm and drastically increased the chemical input, the operator was fortunately sitting in front of the screen and was surprised that someone had taken over his mouse. Moreover, the attacker left the system immediately after the manipulation. Had the attacker chosen a different time, it is very likely that the manipulation would have been noticed much later. Moreover, if he had kept control of the mouse longer, the operator would not have been able to react immediately.
The fact that the manipulation was discovered in time was a coincidence. When the attacker accessed the system again at 1:30pm and drastically increased the chemical input, the operator was fortunately sitting in front of the screen and was surprised that someone had taken over his mouse. Moreover, the attacker left the system immediately after the manipulation. Had the attacker chosen a different time, it is very likely that the manipulation would have been noticed much later. Moreover, if he had kept control of the mouse longer, the operator would not have been able to react immediately.
Even though no damage was caused by the incident, it shows once again how vulnerable industrial networks are. It also shows how quickly and easily critical infrastructure that serves thousands of people can be targeted for disruption. Real-time detection of attacks should not be left to the chance of a watchful operator. Even if subsequent security layers likely would have reported the massive increase in the chemical sooner or later, it is doubtful that the tampering would have been averted if the attacker had been a bit more sophisticated.
A robust intrusion detection system
The incident underscores the need for an end-to-end intrusion detection system. This must detect and report any changes in critical infrastructure networks in real-time. Network monitoring with anomaly detection would have reported the login on the morning of the incident as suspicious and potentially dangerous. To do this, anomaly detection uses various indicators, such as past behavior of the accessing user account (access time, IP address, access duration) and the actions performed using the account. It would also have identified the actor as malicious if they entered the system through an entirely new account.
In addition, an industrial endpoint protection system would have added the ability to automatically prevent certain operations directly on the remotely controlled assets. These protection mechanisms at the edges of an infrastructure are of particular importance. They are effective where the first access to the system often occurs. As a result, they stop attacks before they progress too far. They also prevent lateral movement of attacks, further reconnaissance of the network and lateral movement across the fleet.
Comprehensive protection
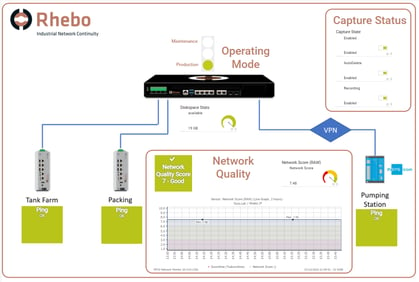
In the past, Rhebo has supported a large number of critical infrastructures in the end-to-end protection of their industrial control systems. As an example: the German water supplier Leipziger Wasserwerke LWW integrated the industrial network monitoring Rhebo Industrial Protector into their security system.
 However, it is not about finding the one measure that fits all. As the threat of exposure and the landscape grow ever more complex, it is about finding the right set of measures. It is a principle of literally all cybersecurity approaches and standards that only a systematic set-up of complementary measures – both organizational as well as technical – can lead to a proper level of security.
However, it is not about finding the one measure that fits all. As the threat of exposure and the landscape grow ever more complex, it is about finding the right set of measures. It is a principle of literally all cybersecurity approaches and standards that only a systematic set-up of complementary measures – both organizational as well as technical – can lead to a proper level of security.
Generally, this principle is called "Defense in Depth", a proven principle for a long time. Think of medieval castles with their hierarchy of walls, gates, narrowings and trenches that ensure that if one measure is breached, the overall structure is still secure. In modern terms of critical infrastructure cyber security, this translates to a combination of risk management, firewalls, VPNs, strong authentication, network segmentation, network and device monitoring (like PRTG) as well as anomaly detection.
Rhebo and PRTG
 Of course the Defense In Depth strategy needs to incorporate Operational Technology (OT) as much as IT. After all, OT is the backbone of daily operation in critical infrastructure. Since OT presents quite different requirements and challenges to enterprise or office IT, it is useful to combine different measures that fit some specific needs of OT. Most of all, this includes ensuring stability through passive approaches that do not disrupt industrial processes.
Of course the Defense In Depth strategy needs to incorporate Operational Technology (OT) as much as IT. After all, OT is the backbone of daily operation in critical infrastructure. Since OT presents quite different requirements and challenges to enterprise or office IT, it is useful to combine different measures that fit some specific needs of OT. Most of all, this includes ensuring stability through passive approaches that do not disrupt industrial processes.
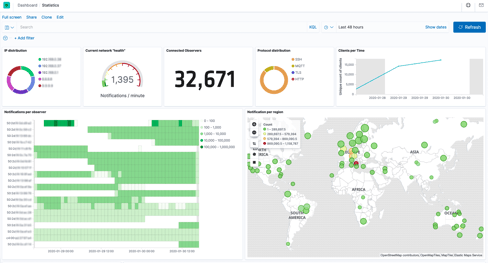
As an example, PRTG and Rhebo Industrial Protector interact in a way that the OT data passively collected by Rhebo with anomaly detection can be used by PRTG (which is by definition an active system) for threat analysis and the definition of counter-measures. Read more about how these two systems can work together.
For more information on the LWW deployment, take a look at the success story on the Rhebo website.
 Published by
Published by